
Trust and compliance.
As the number of connected devices increases, so does the risk of cyber-attacks. We understand your challenges in protecting digital infrastructure, users, and data to stay secured and compliant in a complex threat landscape.
In a connected enterprise, it is not enough to protect data. Every asset including intellectual property, people, processes, and infrastructure runs the risk of a compromise. Therefore, every individual in every department in an organization are responsible and play a role in keeping the digital infrastructure secured.
Compliance to government regulations on data privacy and integrity (such as the GDPR, security directive on NIS) are the undeniable realities of any digital business.
Our security consulting managed, and support services are pro-active and enables you to plan and deploy security program in compliance with industry regulations, and within budget.
Security, trust and compliance.
Keeping pace with the speed of digital transformation initiatives.
Services
We conduct internal and external assessments, perform audits for potential vulnerabilities, provide a risk analysis of exposures in your network infrastructure, and provide lifecycle support and onsite training.
Strategy & Consulting
Achieve your security goals with our network security assessment, security audits, security architecture and design, security platform migrations and DR Strategy Assessment.
Optimization Services
Achieve greater efficiency with our security optimization services that include network security assessment, network security clean-up, and firewall rules clean-up.
Implementation Services
Deploy a robust security framework with our security solutions, security integration, network migration and hardening, security standardization and best practices.
Technical Support Services
Ensure risk mitigation with our lifecycle support functions for security solutions, operation consulting, advisory services, documentation, and onsite training.
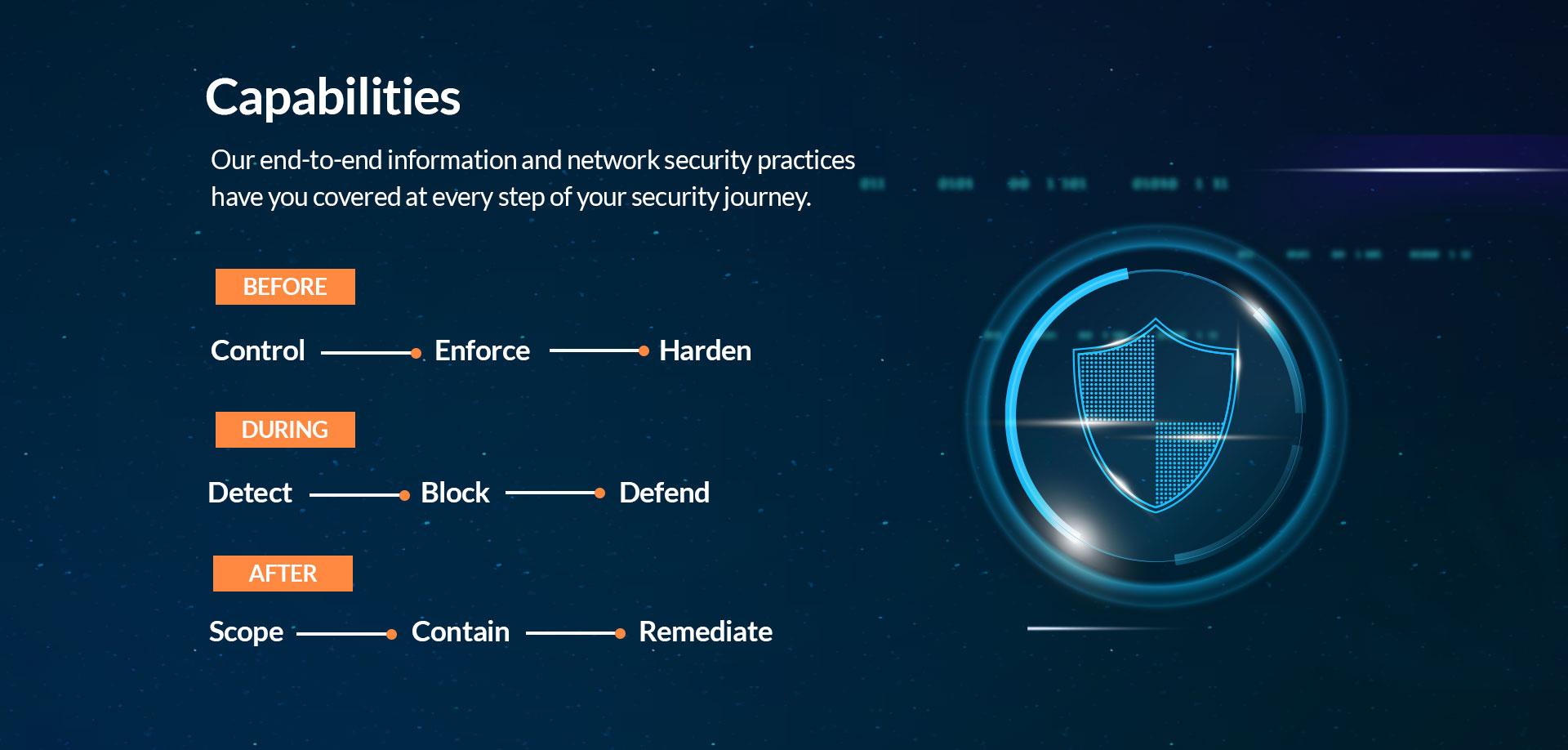
We deliver cost-effective IT security solutions addressing your challenges to remain secure and compliant in a complex threat landscape.
